With the recent leak of Hacking Team’s email archive, the records of their unscrupulous practices are publicly available. I’ve begun to catalog their 0day vendors and purchases (aided by their frequent habit of forwarding sensitive encrypted emails in the clear.) In doing so I ran across Vulnerabilities Brokerage International’s ‘Assets Portfolio’, I believe it’s the most complete list of current and previous 0day to ever become public. The most recent portfolio in the WikiLeaks archive is from October 2014 and it’s available as the attachment from this email.
|
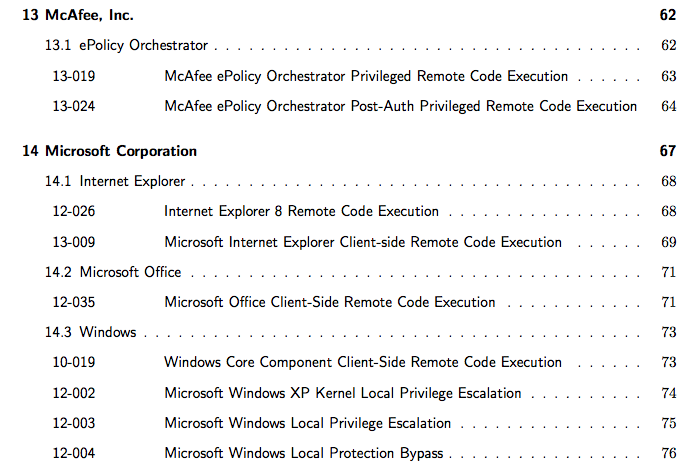
The bulk of the catalog is a listing of available exploits, including the names and versions of the vulnerable software as well as prerequisite access requirements and mitigations bypassed. It also offers a look at the purchasing conditions available in the 0day market. For many of the vulnerabilities listed in the portfolio knowing of their existence doesn’t help in discovering them, vulnerability researchers know that some software (e.g. Flash) will always have more bugs; however, I think the public knowledge that some bugs exist can lead researchers to discover them. For example, the local privilege escalation in OpenPAM (14-001) and the pre-auth remote code execution in Solaris SunSSHD (14-006) offer far smaller code surfaces to analyze along with the knowledge that there is a vulnerability present.
The final section of the portfolio includes a history of most (some names are redacted) of Vulnerabilities Brokerage International’s past vulnerabilities and their availability status. Some that I found interesting include:
- Oracle Solaris SSHD Remote Privileged Command Execution [14-006]
- F5 Networks BIG-IQ Post-auth Remote Privileged Command Execution [13-027]
- GKSu + Oracle VirtualBox Client-side Remote Privileged Command Execution [13-026]
- PHP Remote Command Execution [13-021]
- Apple iOS Remote Forced Firmware Update Avoidance [12-037]
- Apple iOS Remote Forced Access-Point Association [12-036]
- Webmin Remote Code Execution, Information Disclosure [12-005, 12-006, 12-007]
- Nagios Enterprises Nagios XI Remote Code Execution [11-031]
- Apple iTunes Device Update Privilege Escalation [11-021]
- QNX Neutrino RTOS Default Software Local Privilege Escalation [2010-0027, 2010-0028, 2010-0029]
- ESET NOD32 Antivirus and ESET Smart Security Remote Pre-auth Sold Code Execution (as noted by Tavis) [2010-0021]
- AIX Local Privilege Escalation (people are buying AIX LPEs?!) [2010-0005]
Correction 7/10/15 5:10pm: The original blog post referenced ExploitHub as the source of the leak. This was my confusion given Dustin Trammell’s connection to ExploitHub, I have corrected the post to indicate that the source of the portfolio was Vulnerabilities Brokerage International.